The average computer user does not think much about the amount of information they share with others whether in-person, online or at random venues. They just want to be seen and heard because that is how the world works now. If you are not connected to a social media entity, you, my friend, are considered ancient or worse, not one of the “cool kids.” Understandably, some social media interaction is good, but in excess, as with anything, it is not.

Public Service Announcement – This does not happen to the average DOE. However, information gathering is far more easier in today’s social butterfly environment.
Controlling the amount of information an individual or organization discloses in today’s social networking/media world is a difficult task for anyone. In these forums, everyone has a voice. This is a good thing in some regards, but malicious attackers can also take advantage of that voice. People love talking about themselves, making them easy targets for an attacker in various ways, such as scamming, identification (ID) theft, data breaches, etc. These vulnerabilities are even more possible with the constant flow of information over the Internet and the increased use of portable/mobile devices. If you don’t believe me, check your local news tonight.
Attackers are using one of the oldest tricks in the book called Social Engineering, which is the art of skillfully lying to someone to gather information that is considered secret to an individual or organization without their knowledge. In most cases, a victim believes they are just having a general conversation without realizing they have let the attacker know how many kids they have, what school they go to and their personal interests (i.e. soccer, gardening, art, etc.). Yes, I know what you are thinking: Jedi mind tricks, and again, YES, it does work. As a result, the saying STICKS and STONE may break my bones but WORDS will never hurt me is no longer accurate because the WORDS are now able to be communicated around the world in less than a second. Thanks to the internet and social media, we see an increase in data breaches, cyber-bullying, scams, scams and more scams being reported daily throughout the world.
Companies are trying to remediate these issues by attempting to protect their customers’ data and by offering identity protection services to its customers when a data breach occurs. Let’s be real though, how effective is that when the data breach took place 3 months to a year ago (like in the case with the department stores)? After the damage has been done, individuals are looking for services or technology to help them protect their data with either cloud services or crazy amounts of portable storage devices. Again, relying solely on technology to provide protection and not addressing the root cause: the HUMAN error of providing private information through social engineering. People really need to develop a filter or awareness in what they share. Individuals are now taking the same approach to their real lives by disclosing personal information in ways that could potentially put them and their families in harm’s way just to get free stuff or check in on social media to share their location. In addition, customization of license plates, car decals depicting the family members (to include pets), honor roll student stickers, and political view decals give an attacker a good amount of information to start with making “YOU TOO EASY”. This type of sharing should be minimal and monitored, so use DISCRETION as PROTECTION.
In the scenario below, here is how lack of discretion could impact an individual being targeted (keep in mind that this is purely a scenario based example).
James Wilson is a vice president for a financial company who believes in personalizing his achievements in life. When asked about the necessity of sharing, James states that people should be able to express themselves freely and that sharing personal information lets people know in every which way. There’s nothing wrong with that being his response, but when does sharing become over sharing? This is how an attacker could exploit James and his company based off the information he decided to share.
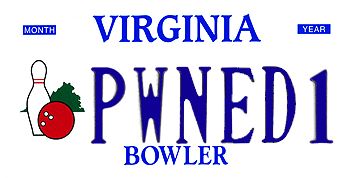
James changed his standard license plates to a customizable version. This makes identifying the vehicle and the driver easy for an attacker. He may share publicly that one of his favorite hobbies is bowling. So now an attacker knows how he often spends his free time and can use that information to determine his passwords or passphrases and exploit him
An attacker could possibly gather information from the local Department of Motor Vehicles (DMV) site or other Personal Information searching databases, which could include:
- Home Address
- Date of Birth
- Driver’s License number
- Expiration Date
If the attacker is skilled enough to gather this information from the local DMV office, then he/she could follow James home. Again, identification of the vehicle is easy to spot. From this point, the attacker could access James’ home purchase information from the internet based on the address. Sorry to say, but this is PUBLIC record; therefore, the attacker would be able to retrieve all information about the residence and residents. This makes ID theft easy given all the information that could be acquired from you or a hacked from a database that stores your personal identification information (PII).
Let’s say James is also a PROUD father of four beautiful kids and his favorite movie is Star Wars. How do I know this, you ask? This decal appears on the back window of his car. These characteristics could reveal a number of features about James to a malicious attacker.
An attacker could discover the number people in his family and their genders and the number of individuals at his home in a particular time period. An attacker could also determine that James may be a techy based on the Star Wars depiction on his vehicle

This could also lead an attacker to assume that James has a lot of valuable gadgets, which could encourage stealing.
The attacker could narrow down James’ answer to security questions for his bank account and other account logins based on the Star Wars reference or bowling interest.
James rocks his bumper sticker letting everyone know that his kids are the smartest Padawan learners (to protect the innocent, insert school name here. He is also proudly promoting the local elementary school his kids attend.

Due to James’ public sharing, he has put his family at risk by providing details about where his kids attend school. An attacker can use this information to kidnap his kids for ransom or for his company’s trade secrets, blackmail him for financial gain, or infiltrate his family by pretending to know his son or daughter to gain further information about James and his family from neighbors. Neighbors tend to give out information about you when the person asking seems to know you. Hence the Jedi mind tricks.
By providing these nuggets of information, a targeted attack is possible based on the information disclosed about oneself. The amount of information disclosed could include an individual’s political views, favorite activities, job resume (with home address) and much more. Again, this information could provide a motivated attacker all the fuel they need to exploit you and your organization. So, the question is, do you want anyone to be able to profile you based on the information you provided? Here are some things you can do to protection yourself against social engineering:
- Stop being so friendly. (I know), just be careful.
- Know the time and place for appropriate conversations.
- Be aware that not all information should be shared with the world.
- Make sure you are able to identify when too much information is being provided to unauthorized persons, oversharing will hurt you!
- Be in control of the conversation flow; shift the conversation to the other person.
- Work on non-verbal response (i.e. this can confirm an answer to a question without a word being said).
This awareness and mindfulness about what is shared with the world can reduce the likelihood of an attacker taking advantage on the HUMAN vulnerabilities through Social Engineering. Keep in mind, many are willing to share all this information with the unknown, not many are willing to pay the price for unauthorized breaches or loss of privacy when an attacker uses their information to exploit them. This is not to say you should STOP sharing things with people in-person or on social media, but DISCRETION is your best PROTECTION. USE IT!!!!